

矢量地理数据密级标识方法研究
作者简介:李梦圆(1992-),女,硕士生,研究方向为三维地质建模。E-mail:myli_92@hotmail.com
收稿日期: 2016-06-01
要求修回日期: 2016-08-16
网络出版日期: 2017-03-20
基金资助
国家自然科学基金项目(41371374、41471175)
国家“863”重大项目子课题(2008AA121604)
江苏高校优势学科建设工程资助项目(PAPD)
Study on Secret Classification Marking Method for Vector Geographic Data
Received date: 2016-06-01
Request revised date: 2016-08-16
Online published: 2017-03-20
Copyright
密级标识是用于标识信息产品安全等级的隐蔽信息,是信息分级管理、控制与应用的基础和前提。作为涉密地理信息产品主要组织格式的矢量地理数据,其密级标识方法的研究具有重要意义。结合矢量地理数据在遭受几何攻击时,其要素空间关系不变性特征,以及密级标识方法的不可感知性、高鲁棒性要求,本文提出一种基于距离比值调制的矢量地理数据密级标识方法,以实现矢量地理数据的分级管理与保护。其主要研究思路为:① 基于距离比值调制的方法,能够较好地应对几何攻击;② 在每个线面要素内,通过重复嵌入密级标识,有效提高算法对于编辑操作的鲁棒性;③ 运用道格拉斯-普克算法提取特征点,在此基础上进行密级标识的嵌入,能够较好地对抗压缩攻击。实验结果表明:该方法具有良好的不可感知性;同时,对嵌入密级标识后的矢量地理数据进行几何变换、数据编辑、数据压缩等攻击后,其密级标识的提取率能够达到80%以上,表明方法具有较好的鲁棒性。
李梦圆 , 李安波 , 周卫 , 蒋伟 . 矢量地理数据密级标识方法研究[J]. 地球信息科学学报, 2017 , 19(3) : 298 -306 . DOI: 10.3724/SP.J.1047.2017.00298
Secret classification marking is hidden information used to mark the security level of information products and is the basis and precondition for classification management, control and application of information. Since vector geographic data is the main organization format of classified geographic information products, it is of great significance to study secret classification marking method for vector geographic data. When suffered from geometry attack, the spatial relationship among elements of vector geographic data is invariable and secret classification marking method requires good imperceptibility and high robustness. In order to realize classification management and protection of vector geographic data, this paper presents a secret classification marking method for vector geographic data based on distance ratio modulating. In essence, using the digital watermark technology, the method embeds secret classification marking as watermarking information into vector geographic data, which has important application value for security protection of vector geographic data. The main ideas related to the study are as follows: Firstly, the method is based on distance ratio modulating and it can deal with geometry attack very well. Secondly, the method effectively improves the robustness against editing attack by repeatedly embedding secret classification marking within each line and area. Lastly, through embedding secret classification marking into feature points which are extracted by using Douglas-Pecker algorithm, the method can also effectively resist data compression attack. The experimental results show that the proposed method has good imperceptibility. In addition, when vector geographic data is suffered from the attacks, such as geometric transformation, data editing and data compression, the extraction ratio of its secret classification marking can reach almost more than 80%, indicating the robustness of this method.
Fig. 1 Basic idea of the algorithm图1 算法基本思路 |
Fig. 2 Generation of the secret classification marking图2 密级标识的生成 |
 ,再根据式(2)计算距离比值r。
,再根据式(2)计算距离比值r。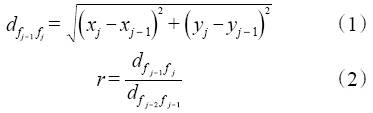
 ,再根据式(2)计算距离比值r'。
,再根据式(2)计算距离比值r'。Fig. 3 Reading and writing of vector geographic data based on OGR图3 基于OGR的矢量地理数据的读写 |
Fig. 4 The experimental data图4 实验数据 |
Tab. 1 The relevant indicators of precision analysis表1 精度分析的相关指标 |
| 调制位 | RMSE.X | RMSE.Y | 最大X误差 | 最大Y误差 |
|---|---|---|---|---|
| 6 7 8 | 0.67E-4 0.63E-5 0.66E-6 | 0.12E-3 0.88E-5 0.99E-6 | 0.00516 0.00034 0.00004 | 0.01047 0.00070 0.00008 |
Fig. 5 The vector map of embedding secret classification marking after geometry attack图5 几何攻击后嵌入密级标识的矢量图 |
Fig. 6 Five kinds of cropping patterns图6 5种裁剪模式 |
Tab. 2 The robustness of secret classification marking after geometry attack表2 几何攻击的鲁棒性 |
| 攻击方式 | 攻击模式 | 变换因子 | 提取率/% |
|---|---|---|---|
| 缩放 | A1 | 0.2 | 98 |
| A2 | 0.5 | 99 | |
| A3 | 2 | 99 | |
| 平移 | B1 | 1E+2 | 99 |
| B2 | 1E+5 | 99 | |
| B3 | 1E+7 | 96 | |
| 旋转 | C1 | 60° | 99 |
| C2 | 90° | 99 | |
| C3 | 150° | 99 |
Tab. 3 The robustness of secret classification marking after cropping attack表3 裁剪攻击的鲁棒性 |
| 裁剪模式 | 裁剪后要素数/个 | 裁剪后点数/个 | 提取率/% |
|---|---|---|---|
| D1 D2 D3 D4 D5 | 89 74 193 131 198 | 1636 1465 3216 2231 3487 | 84 90 81 83 88 |
Tab. 4 The robustness of secret classification marking after adding or removing points表4 增、删点攻击的鲁棒性 |
| 编辑模式 | 原点数/个 | 编辑点数(占总点数百分比) | 提取率/% |
|---|---|---|---|
| 数据增点 | 10 609 | 531(5%) | 88 |
| 10 609 | 1061(10%) | 81 | |
| 10 609 | 3183(30%) | 63 | |
| 数据删点 | 10 609 | 531(5%) | 93 |
| 10 609 | 1061(10%) | 88 | |
| 10 609 | 3183(30%) | 69 |
Tab. 5 The robustness of secret classification marking after data compression attack表5 压缩攻击的鲁棒性 |
| 原点数/个 | 压缩阈值 | 压缩后点数/个 | 压缩率/% | 提取率/% |
|---|---|---|---|---|
| 10 609 10 609 10 609 10 609 10 609 | 1.0 2.5 3.0 3.2 3.5 | 5942 4048 3753 3658 3546 | 56 38 35 34 33 | 96 99 100 89 75 |
Tab. 6 The robustness of secret classification marking after projection transformation attack表6 投影变换攻击的鲁棒性 |
| 攻击方式 | 提取率/% | 还原后提取率/% |
|---|---|---|
| Lambert 投影变换 Mercator 投影变换 | 0 0 | 99 99 |
Tab. 7 The robustness of secret classification marking after combination attack表7 组合攻击的鲁棒性 |
| 组合类型 | 压缩阈值 | 压缩后点数/个 | 变换因子 | 裁剪后点数/个 | 提取率 /% |
|---|---|---|---|---|---|
| 压缩+缩放 压缩+裁剪 平移+裁剪 压缩+平移+裁剪 | 1.0 1.0 - 1.0 | 5942 5942 - 5942 | 2 - 1E+2 1E+2 | - 868 1465 868 | 提取失败 87 90 87 |
Fig. 7 Detecting threshold by exhaustive method图7 穷举法探测阈值 |
Fig. 8 The relationship between data size and consuming time图8 数据量与耗时关系 |
The authors have declared that no competing interests exist.
| [1] |
[
|
| [2] |
[
|
| [3] |
|
| [4] |
[
|
| [5] |
Office for Official Publications of the European Communities, Information Technology Secret Evaluation Criteria[Z]. 1991.
|
| [6] |
FIPS PUB 199, Standards for Secret Categorization of Federal Information and Information Systems[Z]. 2003.
|
| [7] |
BMB17-2006.涉及国家秘密的信息系统分级保护技术要求[S].2006.
[BMB17-2006. Technical requirements for classification protection of information system involves state secrets[S].2006. ]
|
| [8] |
BMB22-2007.涉及国家秘密的信息系统分级保护测评指南BMB22-2007.涉及国家秘密的信息系统分级保护测评指南[S].2007.
[BMB22-2007. Assessment guidelines for classification protection of information system involves state secretsBMB22-2007. Assessment guidelines for classification protection of information system involves state secrets[S].2007. ]
|
| [9] |
[
|
| [10] |
[
|
| [11] |
[
|
| [12] |
[
|
| [13] |
[
|
| [14] |
[
|
| [15] |
[
|
| [16] |
[
|
| [17] |
[
|
| [18] |
[
|
| [19] |
[
|
| [20] |
|
| [21] |
|
| [22] |
第七届全国人民代表大会常务委员会第三次会议.中华人民共和国保守国家秘密法[Z].1988.
[ The Third Session of the Seventh Standing Committee of the National People's Congress. Law on Guarding State Secrets of The People's Republic of China[Z]. 1988. ]
|
| [23] |
国家保密局.国家秘密保密期限的规定[Z].1990.
[ State Secrets Bureau. The provisions of secrecy periods of state secrets[Z]. 1990. ]
|
| [24] |
国家保密局,国家技术监督局.国家秘密文件、资料和其他物品标志的规定[Z].1990.
[State Secrets Bureau,State Bureau of Technical Supervision. The provisions of marking for documents, information and other items of state secrets[Z]. 1990. ]
|
| [25] |
国家测绘局,国家保密局.测绘管理工作国家秘密范围的规定[Z].2003.
[State Bureau of Surveying and Mapping, State Secrets Bureau. The provisions of the scope of state secrets in the management of surveying and mapping work[Z]. 2003. ]
|
| [26] |
CH/T 1030-2012.基础测绘项目文件归档技术规定H/T 1030-2012.基础测绘项目文件归档技术规定[S].2012.
[CH/T 1030-2012. The provisions of filing technology for basic survey-mapping projectsH/T 1030-2012. The provisions of filing technology for basic survey-mapping projects[S].2012. ]
|
| [27] |
|
| [28] |
|
| [29] |
[
|
| [30] |
[
|
| [31] |
[
|
/
| 〈 |
|
〉 |